We have all done it. We’ve gone and installed Google Chrome on our Work PC, Home Laptop, Smartphone, Tablet and Smart TV. You name the platform and Google Chrome is likely there. Some organisations even encourage the use of Google Chrome as it plays nice with the organisation’s web applications. If I’m honest I’m an avid Chrome user myself. I also see a potential problem with Chrome being used in the enterprise.

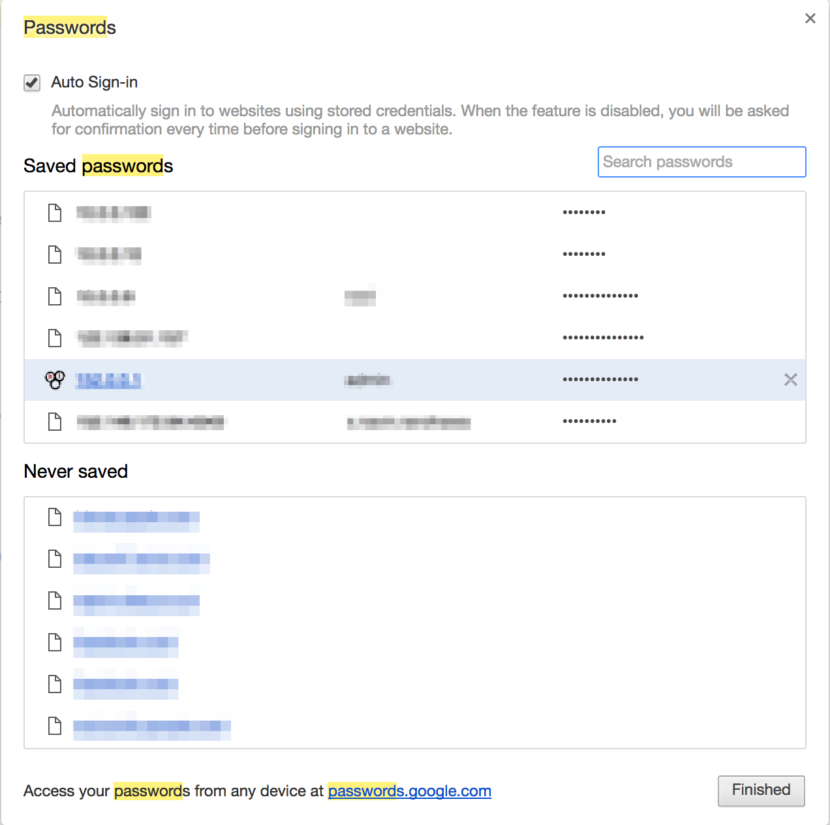
There is no problem with the widespread use of Chrome as an application. The problem lies where you mix business and pleasure. On numerous occasions I’ve seen users signed on to their Chrome browser at work using their personal Google account. This isn’t terribly worrying at first but when you remember that handy password auto fill feature that Chrome has you may start to panic. Although most other browsers also have this feature, none of them integrate as tightly as Google Chrome does with a personal account. Chrome effortlessly syncs across the Password Autofill data across your Chrome browsers so that you never really have to type in a password.
Lets imagine the scenario where we have a privileged user. This user could have access to a couple of web based systems that are internet facing. Lets also say this user is using Chrome linked to his personal Google account and has a habit of saving all his password. There are chances that these web based systems use a non centralised user database (e.g. not AD integrated). This user has now left the company and their user account has been disabled. The user accidentally or purposefully accesses the internet facing company web application from home and low and behold he is allowed straight through and didn’t even have to remember his password.
Worse still, an old exploit where malicious/phishing sites containing hidden text boxes seem to be on the rise. This hidden text boxes leverage your browsers Auto-Fill data and steals your information with out you knowing! Take a look at the below link:
Summarising the “Google Chrome in the Enterprise” issues:
- User Access: When a user leaves an organisation you must make sure to disable ALL user access. Just disabling an AD account may not be the end of it.
- Mitigation: Good practice would be to integrate authentication for all apps against AD. If this is not possible administrators should keep records of what ad hoc access has been provided to non AD integrated systems so this can be referenced when disabling the user.
- Chrome GPO: Google Chrome seems to slip under the radar as a friendly application. Google Chrome should be managed in some form when used in an Enterprise environment.
- Mitigation: If in a Windows environment, administrators can use Group Policy to lock down Chrome prevent data loss.
- AutoFill Phishing Attack: AutoFill in itself can be used maliciously by rouge websites that have hidden text fields designed to steal your autofill data.
- Mitigation: This is slightly tricker and unfortunately down to website reputability and user awareness. The best mitigation against Phishing attacks is user training. Make sure your users can decipher between safe and unsafe websites!
Please do feel free to leave any comments below or share as you please.